TREND AND INSIGHTS
Commercial satellites: the primary target of cyberattacks
With more than 17,800 objects in orbit and over 10,700 active satellites – more than 60% of which are operated by private companies – the commercial space sector has become a backbone for countless essential services, ranging from internet access to navigation, and from critical communications to precision farming. However, this growing reliance exposes satellite systems to an ever-changing landscape of cyber threats, with potentially damaging consequences for society.
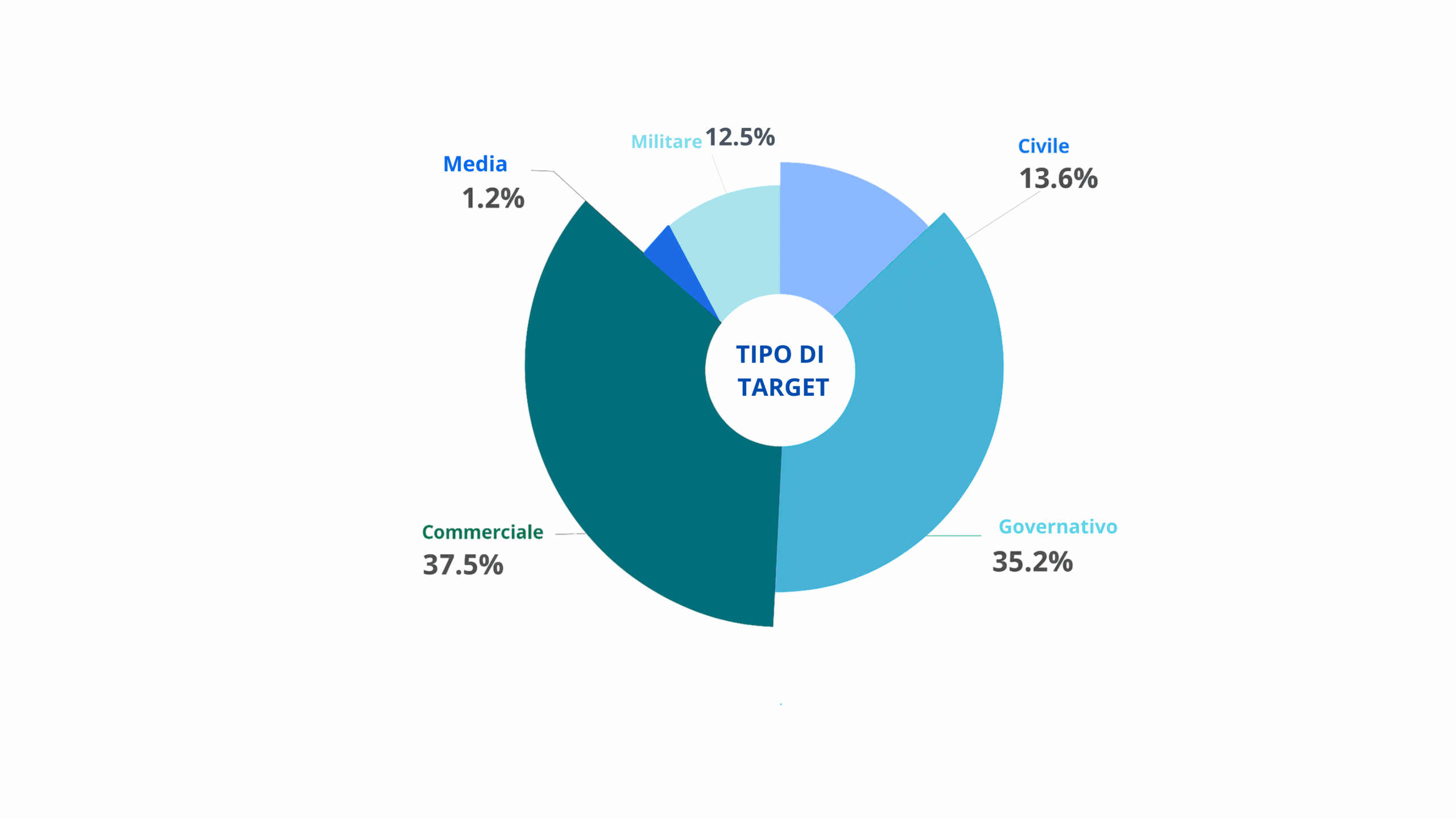
This is the finding of a new report by the European Union Agency for Cybersecurity (ENISA), entitled “Space Threat Landscape” and published in March 2025. The report highlights that, by combining the findings of the “Space Attacks Open Database Project” from 1977 to 2019 with additional information from publicly available reports on individual cyber security incidents in the space domain, commercial satellites emerge as one of the most frequently targeted categories, accounting for approximately 37.5% of known attacks, followed by government targets (35.2%) and, at a considerable distance, by civilian (13.6%) and military (12.5%) targets. The number of attacks against state-run media outlets remains negligible.
Incidents such as the attack on the Viasat satellite in 2022, which disrupted tens of thousands of modems across Europe and caused disruption to emergency services, demonstrate the vulnerability of these systems on a large scale. The repercussions of a successful cyber-attack can be far-reaching and include physical damage, immediate and significant financial losses, social and human impacts, and legal and regulatory consequences.
The report also highlights several key challenges for the cybersecurity of commercial satellites, such as:
- reduce dependence on large global supply chains.
- the use of Commercial Off-the-Shelf components, i.e. components available on the market, which can introduce vulnerabilities if not properly analysed and tested.
- problems with updates due to the remote nature of space-based systems.
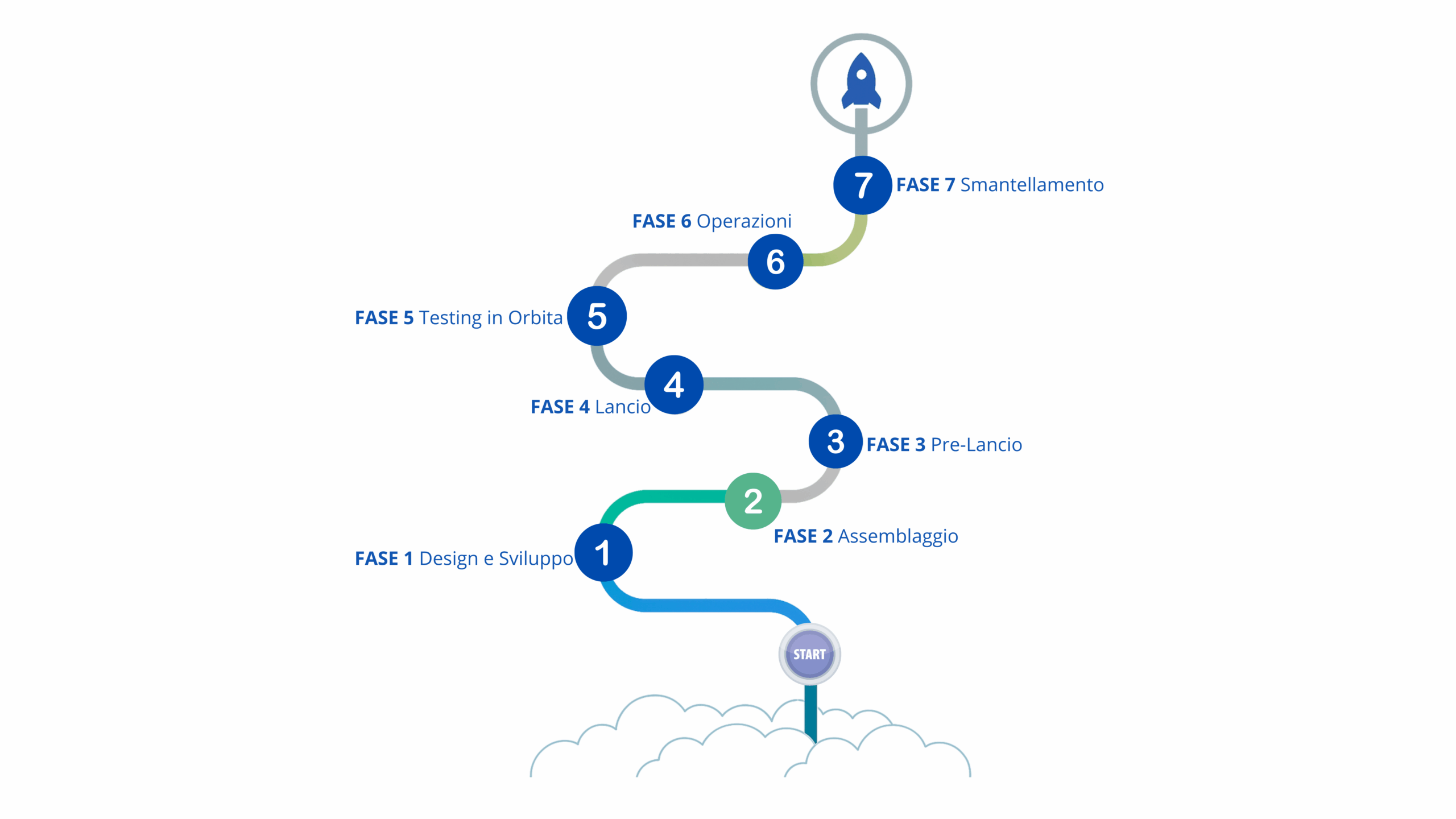
- The high level of human involvement at every stage of the satellite’s lifecycle could introduce risks of configuration errors and internal threats.
- the increasing sophistication of cyber-attacks by highly capable players, including those linked to national states.
To address these challenges, ENISA recommends a holistic approach that includes the implementation of ‘security by default and by design’ principles, rigorous analysis and testing of COTS components, the adoption of robust cryptographic technologies and system segmentation, as well as regular patching and the adoption of a ‘zero-trust’ approach. Cooperation and the sharing of information between operators and the relevant authorities are considered essential for building resilience.
Cyber-skills gap: a strategic risk for the companies
More than three-quarters of the companies are investing in upskilling their staff in digital cybersecurity skills in 2024, as disclosed by Global Cybersecurity Outlook 2025 published by the World Economic Forum in collaboration with Accenture. The survey, in which over 400 companies from 57 countries took part, reveals an increasingly fragmented and complex digital landscape in which the cyber skills gap stands out as one of the main challenges. The lack of specialist expertise acts as a catalyst for risk and vulnerability, limiting companies’ ability to respond effectively and promptly to threats.
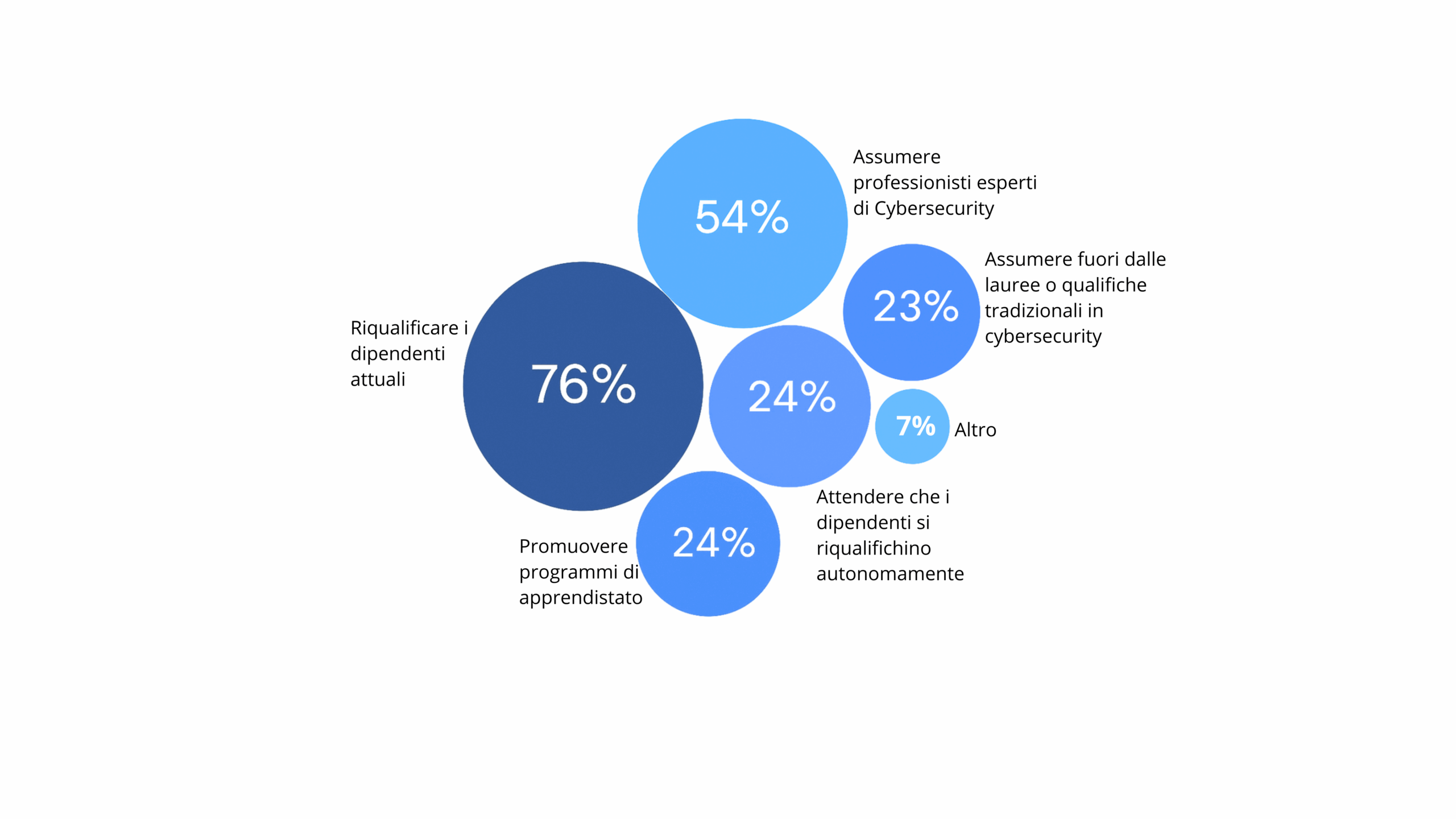
In addition to upskilling, 56% of the companies surveyed are recruiting specialist staff. Other initiatives mentioned include apprenticeship schemes (24%), the recruitment of candidates from non-traditional IT backgrounds (23%) and support for self-directed learning (24%). However, these measures are often inconsistent and inadequate: 69% of small organisations, for example, lack adequate safeguards for the secure adoption of artificial intelligence, whilst 35% report that they do not have an adequate level of cyber resilience — a figure seven times higher than in 2022.
Artificial intelligence, particularly generative AI, represents a key vulnerability. Whilst it offers advanced tools for strengthening defences, it is also being used with increasing effectiveness by malicious actors to automate and amplify attacks, particularly those based on phishing and social engineering. 42% of organisations have already reported incidents of this kind in the past year. Despite this, only 37% of businesses have formal processes in place to assess the risks associated with adopting AI before it is implemented.
The emerging pattern is clear: the complexity of cyberspace is no longer an exception, but a structural feature. In this context, the skills gap acts as a constraint on the ability to respond, which is particularly critical for smaller organisations. Tackling this challenge requires coordinated action, targeted investment in human capital and closer cooperation between the public and private sectors, to ensure the operational continuity and resilience of digital infrastructure in the face of constantly evolving threats.